News & Events
Events
There are currently no upcoming events
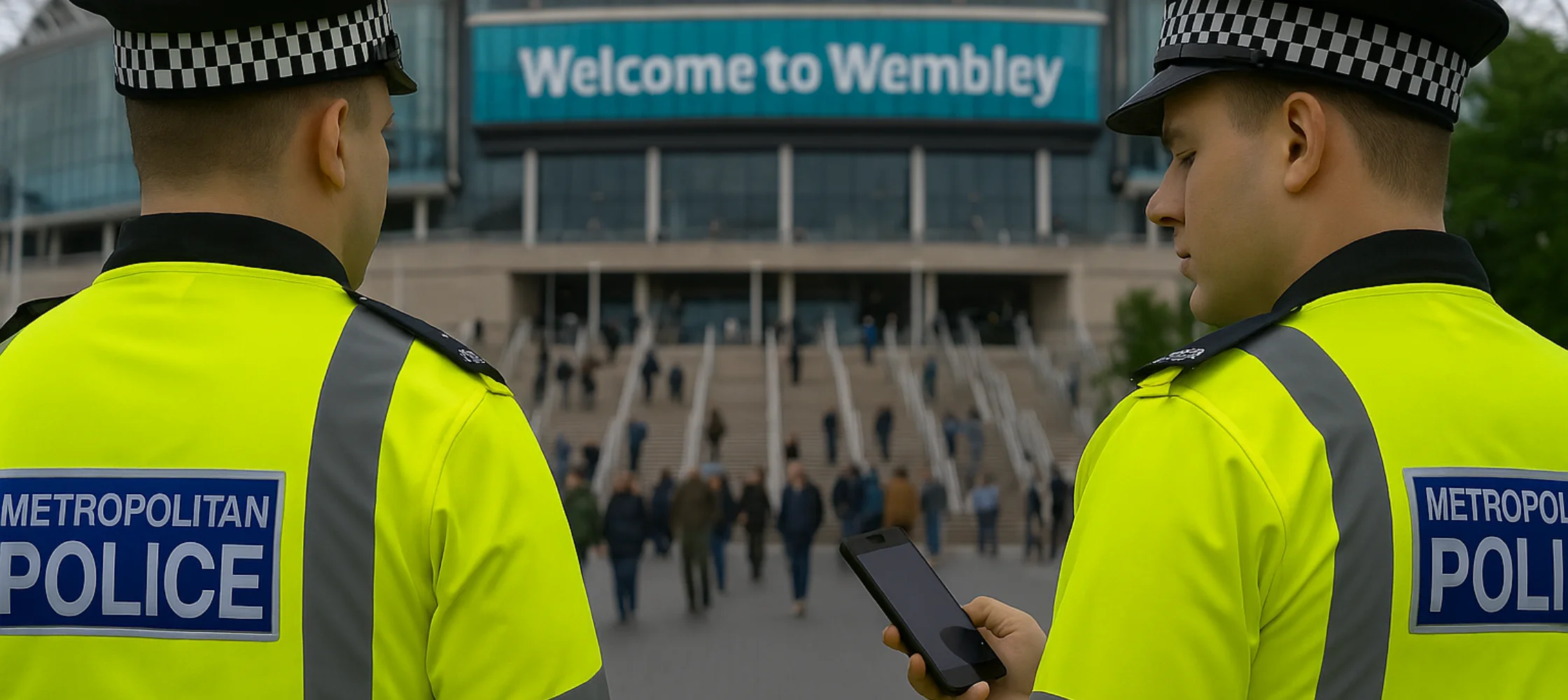
Protecting Public Spaces Under Martyn’s Law
A Response to the Unthinkable Following the devastating Manchester Arena [...]
Physical Security Designed to Last
Need strategies to protect your physical security investments? Keep [...]
The Ultimate Guide to AI-Driven Video Surveillance Solutions
The development, implementation, and operation of bespoke video surveillance [...]
From Keys to Biometric Readers: Evolution of Access Control
Access control technologies and principles are essential for ensuring [...]
3 Practical Tips for Better IT and Security Team Integration
The Need for Collaboration Physical security and IT convergence [...]
Maximizing Government Contracts with NDAA Section 889 Compliance
The National Defense Authorization Act (NDAA) is a critical [...]